Observability
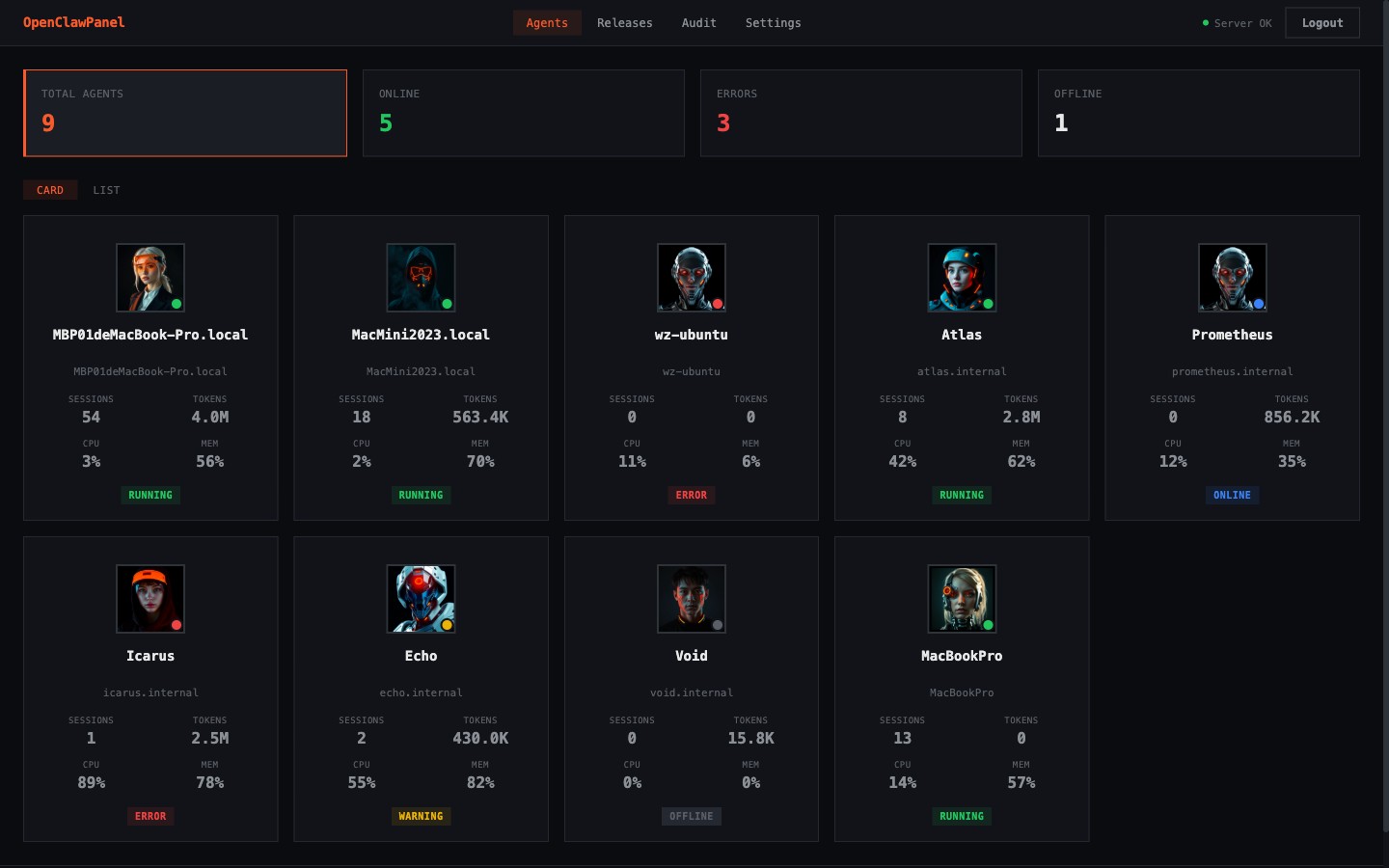
Track OpenClaw health, agent status, sessions, logs, incidents, and host pressure without stitching together separate tools.
Official site for OpenClaw operations
OpenClawPanel helps teams operate the OpenClaw services behind digital employee products: observe health, control runtime actions, recover from incidents, and audit every critical change from one surface.
OpenClaw Fleet
Ops Loop
Core capabilities
Observability
Track OpenClaw health, agent status, sessions, logs, incidents, and host pressure without stitching together separate tools.
Command
Restart, upgrade, snapshot, restore, and intervene across OpenClaw nodes and agents from one surface when the runtime starts drifting.
Recovery
Turn incidents into an operational loop with snapshots, rollback paths, restarts, and recovery actions designed for live OpenClaw services.
Audit
Keep a human-readable record of who changed what, what ran, and what failed when OpenClaw operations stop being casual experiments.
What operations teams actually need
The product is strongest when it closes the loop from installation to incident response. Every important action should be traceable, intentional, and reversible for the teams operating OpenClaw in production.
Issue the runtime token only after an operator explicitly accepts the node.
Recover a degraded OpenClaw node before runtime state drifts any further.
Keep operator actions, rollout state, and incident movement visible after the fact.
Architecture
Agent probe
Collects OpenClaw status, reports events, rotates logs, executes commands, and handles agent self-upgrade without dragging in extra dependencies.
Panel server
Stores the operational truth in SQLite, serves the panel, tracks releases, and returns commands on heartbeat so the network model stays simple.
Operational path
Agents register in pending state first. Admin approval issues the runtime token and turns a raw host into a managed OpenClaw node.
See session pressure, runtime drift, and OpenClaw status without logging into every box by hand.
When a node stalls, the panel gives you restart, snapshot, rollback, and command history instead of blind SSH guesswork.
Deploy story
The official website can live on Cloudflare Pages as an SSR site, while OpenClawPanel continues to run as the operations control plane for your OpenClaw services. The split keeps the public surface fast and the product surface operational.
marketing: openclaw-panel.com app: app.openclaw-panel.com docs: docs.openclaw-panel.com build: npm run build publish: wrangler pages deploy dist --project-name openclaw-panel-site